STUDYING COMPARATIVE CLOUD COMPUTING TECHNOLOGY
Keywords:
Internet of Things (IoT), cloud technologies, cyber attacksDOI:
https://doi.org/10.17654/0973700623003Abstract
In order to provide quicker innovation, adaptable resources, and scale economies, cloud computing is the supply of computing services, including servers, storage, databases, networking, software, analytics, and intelligence, over the Internet. As technology advanced in recent years, cloud technologies were increasingly utilized. Cloud technologies are appealing because data may be stored, transmitted to numerous locations at once, and accessed at any time. It is a system that enables data storage on the Internet, releasing users from the constraints of physical settings and storage devices and enabling access from any location at any time.
Received: August 18, 2023
Accepted: October 3, 2023
References
//www.zdnet.com/article/what-is-cloud-computing-everything-you-need-to-know-about-the-cloud/.
https://www.investopedia.com/terms/c/cloud-computing.asp.
M. Koca and I. Avci, Security vulnerabilities in cloud technology, 4th International Latin American Congress on Natural and Applied Sciences, 2023, pp. 176-182.
P. Thakker and G. Japee, Cloud-based accounting technologies: revolutionizing financial management, International Journal of Science, Engineering and Management (IJSEM) 10(6) (2023), 20-26.
M. Sharif, Blockchain and Cloud: Exploring the Intersection of Two Revolutionary Technologies.
file:///C:/Users/mababalle/Downloads/4.2BlockchainandCloud.pdf.
Md. Tahmid, Accounting in the cloud: a new era of streamlining accounting with cloud technology, Journal of Cloud Computing 1 (2023), 1-14.
M. Balakrishnan and S. K. Soam, Cloud computing technologies and its applications in bioinformatics, Information and Knowledge Management, Publisher: NIPA, 2023, pp. 93-100.
M. A. Baballe, A. Hussaini, M. I. Bello and U. S. Musa, Online attacks types of data breach and cyber attack prevention methods, Current Trends in Information Technology 12(2) (2022), 21-26. DOI (Journal):10.37591/CTIT.
M. A. Baballe et al., Management of vulnerabilities in cyber security, Global Journal of Research in Engineering and Computer Sciences 3(2) (2023), 14-18. https://gjrpublication.com/gjrecs/.
M. B. Ahmad et al., Need for security alarm system installation and their challenges faced, International Journal of New Computer Architectures and their Applications (IJNCAA) 9(3) (2019), 68-76.
M. Cavas and M. B. Ahmad, A review advancement of security alarm system using Internet of Things (IoT), International Journal of New Computer Architectures and their Applications (IJNCAA) 9(2) (2019), 38-49.
M. B. Ahmad et al., The various types of sensors used in the security alarm system, International Journal of New Computer Architectures and their Applications (IJNCAA) 9(2) (2019), 50-59.
A. Zainab, I. Amina, M. Abdulmuhaimin, M. A. Baballe and A. S. Sadiku, Contribution of the IoT to the security system, Global Journal of Research in Engineering and Computer Sciences 3(4) (2023), 1-4. https://doi.org/10.5281/zenodo.8161017.
I. Amina, A. S. Sadiku, D. Muntaka, M. Abdulmuhaimin and M. A. Baballe, Modern alarm sensors for security systems, Global Journal of Research in Engineering and Computer Sciences 3(4) (2023), 11-15. https://doi.org/10.5281/zenodo.8193716.
Downloads
Published
Issue
Section
License
Copyright (c) 2023 PUSHPA PUBLISHING HOUSE, PRAYAGRAJ, INDIA

This work is licensed under a Creative Commons Attribution 4.0 International License.
_________________________
Attribution: Credit Pushpa Publishing House as the original publisher, including title and author(s) if applicable.
Non-Commercial Use: For non-commercial purposes only. No commercial activities without explicit permission.
No Derivatives: Modifying or creating derivative works not allowed without written permission.
Contact Puspha Publishing House for more info or permissions.




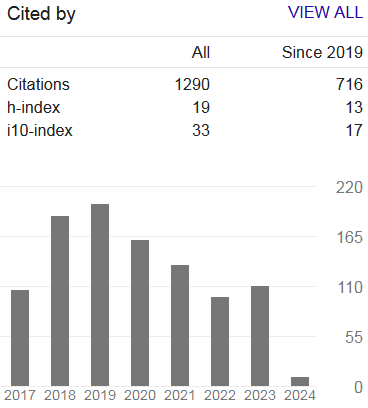
 Google h-index:
Google h-index:  Downloads:
Downloads: