PROXY RE-ENCRYPTION BASED ON THE GENERALIZED EL GAMAL ENCRYPTION SCHEME
Keywords:
cryptography, proxy encryption, access delegation.DOI:
https://doi.org/10.17654/2277141723015Abstract
In 1998, Blaze et al. [10] presented proxy re-encryption as a cryptographic primitive in which a proxy transforms a ciphertext for Alice into one for Bob without seeing the corresponding plaintext and secret keys.
Ateniese et al. [4] proposed in 2005 a formal definition of unidirectional proxy re-encryption and its security guarantees. They build proxy re-encryption schemes based on El Gamal encryption scheme and bilinear pairing.
In this paper, we recall some proxy encryption notions and definitions and propose new unidirectional proxy schemes. Our proxy schemes are variants of Ateniese’s schemes based on the “lite” Cramer-Shoup encryption scheme and the generalized El Gamal encryption scheme.
Received: October 24, 2022;
Accepted: December 30, 2022;
References
Emmanuel Bresson, Dario Catalano and David Pointcheval, A simple public-key cryptosystem with a double trapdoor decryption mechanism and its applications, In Chi-Sung Laih, editor, Advances in Cryptology - ASIACRYPT 2003, Berlin, Heidelberg, Springer Berlin Heidelberg, 2003, pp. 37-54.
Ronald Cramer and Victor Shoup, Design and analysis of practical public-key encryption schemes secure against adaptive chosen ciphertext attack, SIAM Journal on Computing 33(1) (2003), 167-226.
T. El Gamal, A public key cryptosystem and a signature scheme based on discrete logarithms, In CRYPTO, IT-31(4), 4 (1985), 469-472.
G. Ateniese, K. Fu, M. Green and S. Hohenberger, Improved proxy re-encryption schemes with applications to secure distributed storage, In NDSS, 2005, pp. 29 43.
Chunpeng Ge, Willy Susilo, Liming Fang, Jiandong Wang and Yunqing Shi, A CCA-secure key-policy attribute-based proxy re-encryption in the adaptive corruption model for dropbox data sharing system, Designs, Codes and Cryptography 86(11) (2018), 2587-2603.
Anca-Andreea Ivan and Yevgeniy Dodis, Proxy cryptography revisited, In NDSS, Citeseer, 2003.
Markus Jakobsson, On quorum controlled asymmetric proxy re-encryption, In Public Key Cryptography, Berlin Heidelberg, Springer Berlin Heidelberg, 1999, pp. 112-121.
Wei Luo and Wenping Ma, A secure revocable identity-based proxy re-encryption scheme for cloud storage, International Conference on Cloud Computing and Security, Springer, 2018, pp. 519-530.
Ahsan Manzoor, Madhsanka Liyanage, An Braeke, Salil S. Kanhere and Mika Ylianttila, Blockchain based proxy re-encryption scheme for secure Iot data sharing, 2019 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), IEEE, 2019, pp. 99-103.
G. Bleumer, Matt Blaze and M. Strauss, Divertible protocols and atomic proxy cryptography, Proceedings of Eurocrypt 1998, Vol. 1403, 1998, pp. 127-144.
Yuriy Polyakov, Kurt Rohloff, Gyana Sahu and Vinod Vaikuntanathan, Fast proxy re-encryption for publish/subscribe systems, ACM Transactions on Privacy and Security (TOPS) 20(4) (2017), 1-31.
Demba Sow and Djiby Sow, A new variant of El Gamal’s encryption and signatures schemes, JP Journal of Algebra, Number Theory and Applications 20(1) (2011), 21-39.
V. Vijayakumar, M. K. Priyan, Gandhi Ushadevi, R. Varatharajan, Gunasekaran Manogaran and Prathamesh Vijay Tarare, E-health cloud security using timing enabled proxy re-encryption, Mobile Networks and Applications 24(3) (2019), 1034-1045.
Peng Xu, Tengfei Jiao, Qianhong Wu, Wei Wang and Hai Jin, Conditional identity-based broadcast proxy re-encryption and its application to cloud email, IEEE Transactions on Computers 65(1) (2015), 66-79.
Downloads
Published
Issue
Section
License
Copyright (c) 2023 Pushpa Publishing House, Prayagraj, India

This work is licensed under a Creative Commons Attribution 4.0 International License.





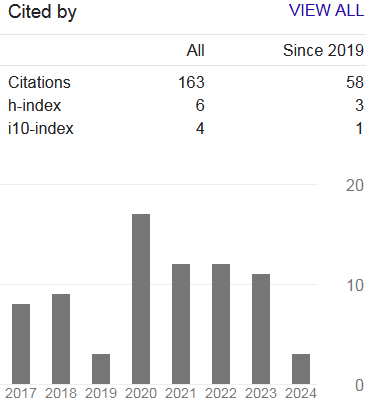
 Google h-index:
Google h-index:  Downloads:
Downloads: 